What is OpenVAS?
OpenVAS, or Open Vulnerability Assessment System, is a powerful tool designed to detect vulnerabilities in software and systems. It facilitates comprehensive vulnerability scanning, enabling organizations to identify weaknesses before malicious actors exploit them. OpenVAS is favored for its versatility, open-source nature, and ability to adapt to diverse environments.
OpenVAS is a vulnerability scanner that uses a variety of methods to identify security weaknesses in systems and applications. These methods include:
- Scanning for known vulnerabilities using a database of over 50,000 vulnerability signatures
- Testing for common misconfigurations
- Conducting web application scans
- Evaluating compliance with security standards
Ways to Use OpenVAS:
Network Vulnerability Scanning: OpenVAS performs in-depth scans of network systems, uncovering potential vulnerabilities in operating systems, applications, and configurations.
Web Application Security Testing: OpenVAS assesses web applications for security weaknesses, including outdated software, misconfigurations, and potential entry points for attacks.
Server Security Audit: It evaluates server setups, analyzing services, settings, and configurations to identify potential entry points for malicious activity.
Compliance Auditing: OpenVAS aids in compliance efforts by identifying security gaps that might violate industry regulations or best practices.
Example of use
A company can use OpenVAS to scan its internal network for vulnerabilities. The scan would identify any systems or applications that are vulnerable to known attacks. The company could then take steps to mitigate these risks, such as patching the vulnerabilities or implementing security controls.
Pros and cons
Pros:
- OpenVAS is free and open-source, so it is a cost-effective option for vulnerability assessment.
- It is a comprehensive solution that can be used to scan networks, web applications, and systems for vulnerabilities.
- It has a large database of vulnerability signatures, so it can identify a wide range of security weaknesses.
- It is easy to use and configure, even for non-technical users.
Cons:
- OpenVAS can be a complex tool to use, and it may require some technical knowledge to configure and interpret the results.
- It is not as powerful as some commercial vulnerability scanners.
- The vulnerability database is not always up-to-date, so it may not identify the latest vulnerabilities.
Setting Up
Installing OpenVAS
To install OpenVAS, you can follow the instructions on the OpenVAS website. The installation process will vary depending on the operating system that you are using.
For Linux:
root@kali:~# apt update && apt upgrade root@kali:~# apt install openvas
Next, start the initial setup of OpenVAS. This downloads all of the up to date vulnerability information from OpenVAS’s community feeds. This process also takes several minutes to complete, so now would also be a good time to go do something else for a while.
root@kali:~# openvas-setup /var/lib/openvas/private/CA created /var/lib/openvas/CA created [i] This script synchronizes an NVT collection with the 'OpenVAS NVT Feed'. [i] The 'OpenVAS NVT Feed' is provided by 'The OpenVAS Project'. [i] Online information about this feed: 'http://www.openvas.org/openvas-nvt-feed.html'. [i] NVT dir: /var/lib/openvas/plugins ... ... Rebuilding NVT cache... done. User created with password 'XXXXXXXX-XXXXX-XXXX-XXXX-XXXXXXXXXXXX'.
Keep note of this password, you will need it next. Browse to https://127.0.0.1:9392 and accept the certificate for OpenVAS. Login as admin with the password provided on the last line of openvas-setup:
Configuring OpenVAS
Once you have installed OpenVAS, you will need to configure it. This includes setting up the database, creating users, and configuring the scanners.
The database is used to store the scan results and vulnerability information. You can use the MySQL or PostgreSQL database for OpenVAS.
You can create users to manage the OpenVAS system. Each user will have different permissions, such as the ability to scan networks, view scan results, and create reports.
The scanners are used to scan networks and systems for vulnerabilities. OpenVAS comes with a variety of scanners, including network scanners, web application scanners, and operating system scanners.
Starting the OpenVAS scanners
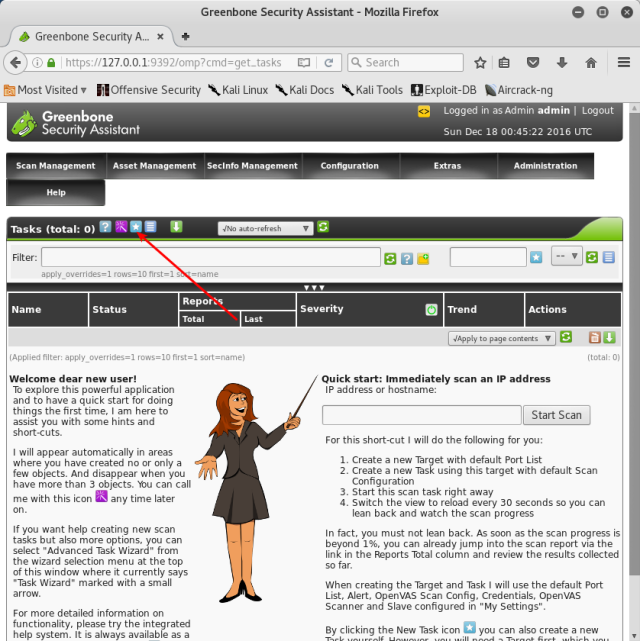
Once you have configured OpenVAS, you can start the scanners. This will begin scanning your network or systems for vulnerabilities.
Configuration -> Targets
Next, fill out the form that appears after you click on the star icon. Give your target a name, comment, and set the host appropriately. In my case, this is 172.16.158.130. I changed the port list to use both TCP and UDP, and left the Alive Test to default. Depending on the circumstances, you may need to change these settings. One common example is that some hosts on a network may not respond to pings due to firewall settings. For these hosts,I set the Alive Test to “Consider Alive” so it scans it even if it is not pinging. Click on Create Target to finish this process. From here, you will need to create a new task. Do this by going to Scan Management -> Tasks and clicking on the blue and white star button to create a new task:
Once your task is created, clicking on Scan Management will bring you to a page with the scan listed. Click on the green and white play button to run this scan right now:
Clicking on Scan Management again brings you back to the same page, but shows the progress of the scan. Clicking on the scan name itself will bring you to a new page that can be configured to refresh automatically:
The scanners will scan the ports and services that are open on your network or systems. They will also look for common vulnerabilities and misconfigurations.
Analyzing the scan results
Once the scans have completed, you can analyze the results. This will help you to identify any vulnerabilities that need to be addressed.
The scan results will be displayed in the OpenVAS web interface. You can use the web interface to filter the results, view detailed information about each vulnerability, and create reports.
Overall, OpenVAS is a powerful and versatile vulnerability scanner that can be used by organizations of all sizes. It is a cost-effective option that can help to identify and mitigate security risks.